Businesses need to work efficiently. Downtime costs companies money in payroll and loss of revenue due to time away from sales, communication, service, etc. Technology is a tool that businesses depend upon and when it is not working many jobs stop immediately. BlueKey IT Services are set up proactively so companies can avoid a technology crisis and downtime when possible. To ensure proactive support, every BlueKey service agreement includes 24/7 monitoring and anti-virus protection along with helpdesk support.
Proactive Support with Anti-Virus Protection
24/7 monitoring and anti-virus protection work proactively on every computer to monitor the health of the computer and block potential viruses from creating havoc on a computer. Viruses cause computers to behave strangely causing the user to spend time trying to figure out the issue, getting popups that distract or take time to figure out how to close them. Even worse viruses can cause issues that make the computer or network unusable. 24/7 monitoring is also proactive as it monitors the health of the computer automatically. Once an issue is found, it can be fixed automatically by the monitoring system in some instances. In other circumstances, TeamBlue is notified of the issue through the monitoring software and can fix the issue on-site or remotely. Either way proactive anti-virus protection and monitoring keeps employees working and avoids downtime.
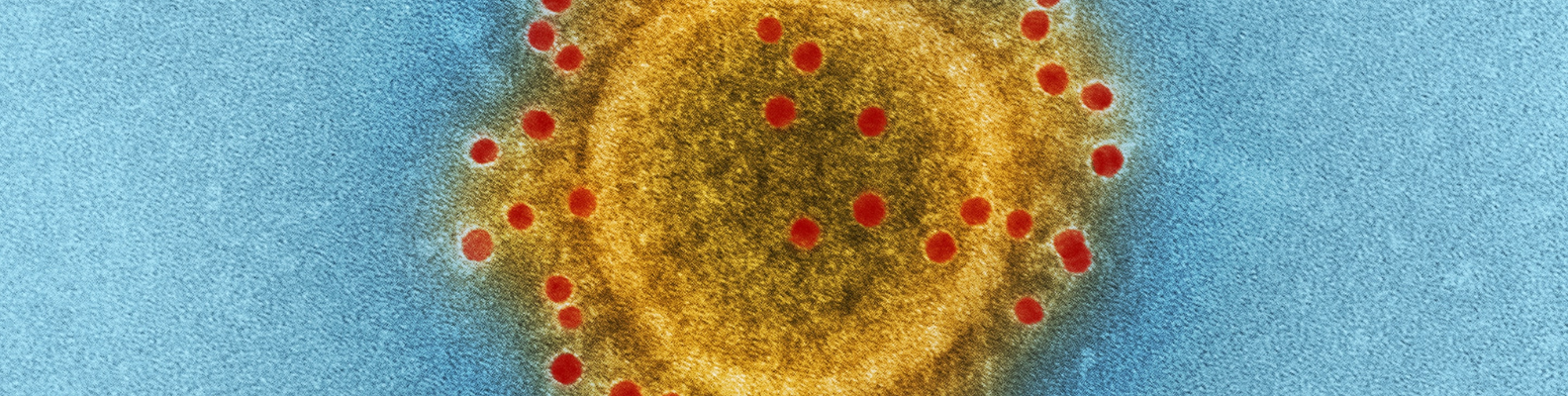
Virtual Threats
Malicious software creators have different intents and malware can look different once it is installed on a computer. Businesses need to be aware of the different types so they can be on the defensive quickly when the computer starts behaving strangely.
Types of Virtual Threats
A virus is malicious code or a program written to alter the way a computer operates and is designed to spread from one computer to another.
Adware is software that automatically displays or downloads advertising material (often unwanted) when a user is online.
Spyware captures information like web browsing habits, e-mail messages, usernames and passwords, and credit card information. If left unchecked, the software can transmit this data to another person’s computer over the Internet
A Trojan Horse is malicious code or software that looks legitimate but can take control of your computer and is designed to damage, disrupt, steal, or in general inflict some other harmful action on your data or network.
Worms are malware that spread copies of itself from computer to computer. A worm can replicate itself without any human interaction.
What Does a Virus Look Like?
A virus can make a computer simply act strangely or be undetectable like spyware. Companies rely on anti-virus protection to protect them against spyware but what does adware look like? Recently BlueKey IT had an example of adware pop up on a computer. The user was complaining that links in Outlook were not opening in the web browser like normal. TeamBlue took a look at the computer. It had been hijacked by adware that changed the default web browser to the adware’s web browser to show advertisements each time the users clicked a link. After a malware scan was run, 24 viruses were discovered and quarantined! Afterwards the computer went back to working well with clickable links in email. Luckily this virus was more of a nuisance and did not infect the network further.

Ransomware
Other more dangerous threats have the potential to destroy all data on the network. Threats like ransomware steal all data, software, operating systems and are spread through the network with great speed. The creators of the virus then contact the business for a sum of money to release the data. Downtime is immediate and companies will not be able to work or even use their computers until the money is paid or the system is recreated. This includes paying for all software again and recreating data that was not backed up. If the data was backed up, the software and data can be saved but will still take time to download from the cloud. Good anti-virus protection can detect the pattern of ransomware and although some data may be lost, most of the software and data will be protected.
How Can Businesses Avoid Threats?
Protecting computers, servers, and network with anti-virus protection is the first line of defense. Anti-virus software constantly searches the device for known malicious software. If it finds a virus, adware, spyware, a Trojan Horse or a worm, it automatically disinfects the computer.
In some circumstances, it will ask the user what he/she would like to do with the malware. Then the user can choose to quarantine the virus or file or let the software know that the software is allowed. Sometimes this happens when a new program is downloaded intentionally by the user but the anti-virus software is concerned about some of the functions of the software. It will want to block the installation and warn the user of a potential threat. BlueKey IT can assist business owners and employees with determining the right balance between protection and usability. The company still needs to function well even though certain elements of software could potentially open the system to threats. TeamBlue can provide security advisement that can use other ways to protect the system if anti-virus protection is not enough.
Threats Are Not Always Avoidable
Malicious software is not always avoidable. The people and organizations that create the threats are constantly creating new software. Some of it is easily identifiable and avoidable. While others can even slide past the best anti-virus protection. Luckily anti-virus software companies are constantly searching and reacting to new threats so they can protect their customers. This along with security patches from updates to Windows operating systems and MAC iOS, protect business computers from most threats. The best way to avoid threats though is to educate staff about how to avoid threats. Then when they happen, to have a BlueKey IT there to clear the threat from the computer or network. Always having off-site backups of data is also vital to being prepared if the worst type of threats thwart all protections and infiltrate the network.
Anti-Virus Protection and BlueKey IT Services
BlueKey IT provides proactive support that includes anti-virus protection to avoid threats to computers, servers and the network. Although some viruses are simply an inconvenience, others have the potential to take down the whole network. TeamBlue wants each client to be able to avoid downtime so provides proactive tools like anti-virus protection to keep employees working without interruption. Interested in learning more about proactive support for your business? Contact BlueKey IT for a free Network Assessment!